PPP configuration in packet tracer
PPP encapsulation is used on the WAN connections, which are offered by the service providers through a leased line.
PPP (Point to Point Protocol) is an industry standard protocol. As a result, this protocol is supported by many vendors that produce the networking devices.
PPP has many features like data compression, authentication and multi-link that make it very popular among the companies.
PPP uses following protocols to support variety of features.
Link Control Protocol (LCP) –
LCP protocol is used by the PPP to establish the connection.
PPP has ability to use following NCPs (Network control protocol)
· Internet Protocol Control Protocol (IPCP)
· OSI Network Layer Control Protocol (OSINLCP)
· Applet talk control protocol (ATCP) and Internetwork Packet Exchange Control Protocol (IPXCP)
· Internetwork Packet Exchange Control Protocol (IPXCP)
· DECnet Phase IV Control Protocol (DNCP)
· NetBIOS Frames Control Protocol (NBFCP)
· IPv6 Control Protocol (IPV6CP)
PPP can use two following protocols for the authentication.
· Password Authentication Protocol (PAP)
PAP provides password based protection to the connection however sends the password in the plain text over the network, which makes it less secure protocol so this protocol should be avoided on highly secured networks as this vulnerability can be easily used by the hacker to break in the network.
· Challenge Handshake Authentication Protocol (CHAP)
This protocol uses three way handshake and uses MD5 hashing to encrypts the plain text. In this type of authentication, peer sends the hash value to the authenticator instead of plain text and then authenticator matches that value with its own calculated hash value to establish the connection.
Authentication happens several times in the already established connection to enhance the security and make sure that the security is not compromised.
CHAP protocol is far better than PAP authentication as encryption makes the password highly secure and even if somebody is using the packet sniffer then only hash value can be captured. Although MD5 does not provide completed protection as there are ways by which someone can reverse engineer the hash to receive the plain text however these techniques are highly complex to use.
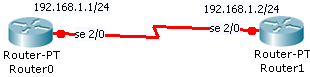
In this lab, we will configure PPP protocols on the routers. PPP should be enabled on both the routers to work, as the routers are required to use the same protocol to establish a connection. Also, we will set up clocking on the router 0 that is connected with DCE side of the cable.
PPP protocol configuration
Lab Tasks
1. Assign IP address to both routers 2. Set PPP encapsulation 3. Set clocking
Lab Configuration
Task 1
Router 0
Router(config)#int se 2/0
Router(config-if)# ip address 192.168.1.1 255.255.255.0
Router(config-if)# no shut
Router 1
Router(config)# int se 2/0
Router(config-if)# ip address 192.168.1.2 255.255.255.0
Router(config-if)# no shut
Task 2
On both routers
Router(config)#in se 2/0
Router(config-if)#encapsulation ppp
n router 0
Router(config)#in se 2/0
Router(config-if)# clock rate 56000