Configure ACL (Acess-list) in packet tracer
In this lab, we will configure ACL in the Cisco packet tracer and we will see how the access list blocks the traffic based on different conditions.
An access list provides the ability to control the traffic in the network. We can set up an access list according to our requirements. The access list filters out traffic based on the configuration.
Cisco router IOS has enough commands through which we can control traffic effectively however special hardware like pix firewall or ASA firewall have many extra security features.
Access list rules or conditions are read series wise so If any network that is denied earlier will not be permitted even after adding the permit statement e.g.
Deny 192.168.1.0 0.0.0.255
Permit host 192.168.1.5
In the above access list rules, we have denied the complete 192.168.1.0 network and in the second rule, we are permitting the host from the same network. As access-list rules are read in the series, the router will drop every packet from this network because it matches the deny rule. The router will read the second rule later but till then the traffic from that network is denied already so we have to be careful when setting up the rules for the access list.
Standard access list vs. extended access-list
Standard access list – Standard access list only filters out traffic based on the source IP. This access list does not have any other way to filter traffic so this provides basic functionality.
Features of standard access list
- A standard access list is very easy to configure.
- It is very light on the processor so it does not overload the hardware.
Extended access list – Extended access lists can filter out traffic based on source IP, destination IP, protocols like TCP, UDP, ICMP, etc, and port numbers.
Feature of extended access list
- It’s not easy to configure as compared to the standard access list however it provides many filters that we can use to control traffic efficiently.
- Requires more processor cycles due to the complexity of the defined rules.
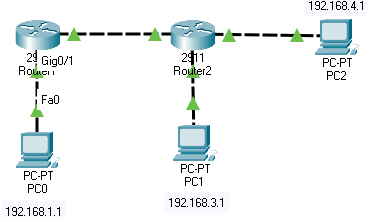
In this Standard Access list configuration, we will block PC0 traffic from reaching router 2
We are using the following commands to create an access list
The standard access list can be given a number from 1-to 99 so we will give the number 1 to our access-list
Router(config)#access-list 1 deny 192.168.1.1
Router(config)#access-list 1 permit any
While creating an access list, we have to make sure to use permit any command to allow other traffic that we don’t want to block because there is an invincible deny at the end of every access list so if this command is missed then the access list will block all traffic.
Now, we have created the access list however it will not work until we apply this to the router’s interface. While enabling access list on the router’s interface, we must make sure that it is being applied to the correct interface and in the right direction, otherwise standard list will not work because it filters traffic according to the source IP.
To apply, we have to use the following command.
Router(config)#interface gigabitEthernet 0/0
Router(config-if)#ip access-group 1 out
An access list is applied to the router’s interface in the inbound and outbound directions. We can only enable 1 access list per interface and direction.
In the above example, an access list is enabled on the gigabit Ethernet port of router 1 in the outbound direction as we want to block traffic from PC0 from reaching router 2.
Once the access list is enabled, we can check if it working appropriately by generating traffic. This can be checked by pinging the router from the host.
Following is the outcome when router 2 pinged from the host.
C:\>ping 192.168.2.2
Pinging 192.168.2.2 with 32 bytes of data:
Reply from 192.168.1.2: Destination host unreachable.
Reply from 192.168.1.2: Destination host unreachable.
Reply from 192.168.1.2: Destination host unreachable.
Reply from 192.168.1.2: Destination host unreachable.
We can use the following command to verify if the access list has blocked packets
Router#show access-lists
Standard IP access list 1
10 deny host 192.168.1.1 (4 match(es))
20 permit any
As seen in the command output, deny condition has blocked the traffic from the host, 4 matches are for those ping packets that were sent to the router.
Configuring Extended Access list in Cisco packet tracer
As we have discussed, an extended access list can filter traffic on a protocol basis so we will block PC2 from pinging all other devices in the network.
We have used the following commands to create the access list
Router(config)#ip access-list extended 100
Router(config-ext-nacl)#deny icmp host 192.168.4.1 any
Router(config-ext-nacl)#permit ip any any
Numbers 100 to 199 are reserved for the extended list. We have chosen the number 100 and added two conditions to the list.
We have applied this access-list in the inbound direction on router 2.
Only ICMP traffic is blocked, this protocol is used for the ping functionality so now PC2 should not be able to ping any device in the network however rest of the traffic is permitted.
We can test the access-list by generating ICMP traffic using the ping command from PC2.
As expected, traffic is blocked by the router. Please check the ping result below
C:\>ping 192.168.4.2
Pinging 192.168.4.2 with 32 bytes of data:
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Ping statistics for 192.168.4.2:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
C:\>ping 192.168.1.1
Pinging 192.168.1.1 with 32 bytes of data:
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Reply from 192.168.4.2: Destination host unreachable.
Ping statistics for 192.168.1.1:
Packets: Sent = 4, Received = 0, Lost = 4 (100% loss),
The access list blocked 8 packets that were generated from PC2
Router#sh access-lists
Extended IP access list 100
10 deny icmp host 192.168.4.1 any (8 match(es))
20 permit ip any any
Cisco ACL practice labs
Using the same lab, complete the following challenges
Task 1
Use a standard access list to block traffic from PC0 to PC2
Task 2
Use extended access list to block DNS traffic generated from PC0 to PC2
Cisco packet tracer traffic generator
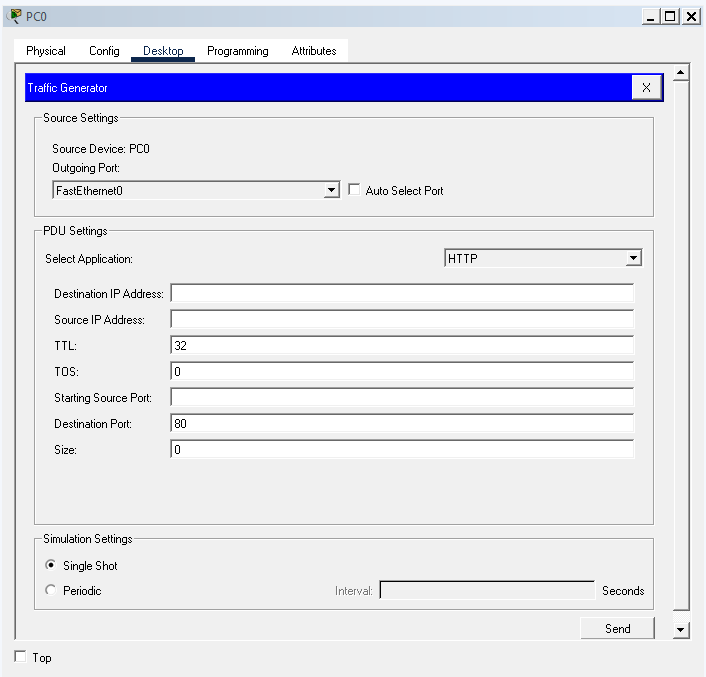
Use the traffic generator tool to generate different types of traffic. This is a great tool for testing access-lists.